Use a Serverless Plugin to check your Git branch before deploying on AWS. In this article, you will see how to write a Serverless plugin that checks your local Git branch before deployment so as to avoid deploying bad code.
If you are curious about the Serverless framework, you can read the article Severless API explaining how to deploy a rest api with Serverless in 15 minutes.
Deploy to the Cloud!
We use the amazing Serverless toolkit to deploy to AWS. We managed the different environments using environment variables as explained in the Serverless documentation.
To deploy to the desired environment, we simply run:
sls deploy --stage TARGET_ENV --aws-profile sicarawhere TARGET_ENV is the target environment e.g., development, staging or production.
The application environments
A development process typically includes the following environments:
- The development environment: This is the environment where the developers run the code they are writing. Because the developers need to test intensively their code, the development environment can be broken sometime — and it is even meant to be.
- The staging environment: This is where the data product owner validates the new features. It should never be broken so that validation can be done at any time. The purpose of this environment is to see the developer's daily work, so features may be partially implemented.
- The production environment: This is the environment for the end-users. It should never be broken and features should be complete.
The problem: you could deploy bad/buggy code
When deploying, local files are zipped and uploaded directly to AWS. There is no control of the local files before there are uploaded, which is fine when deploying to the development environment but wrong for staging or production environment.
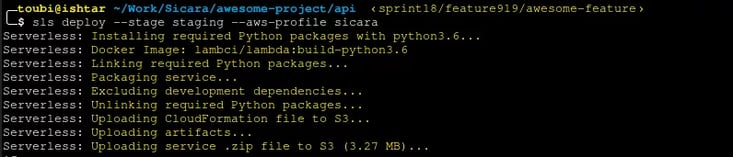
In the screenshot above, the git branch sprint18/feature919/awesome-feature is deployed to the staging environment. This could be wrong for several reasons:
- The branch
sprint18/feature919/awesome-featurehas not yet been merged into themasterbranch, meaning it was not reviewed by the other developers. Thus, it could break the staging environment. - The branch
sprint18/feature919/awesome-featureis local, meaning it does not include features developed by other members of the team. Thus, it could induce regression by making these other features disappearing. - There are pending changes not yet committed. Thus, the deployed code is not versioned and could possibly be lost.
The solution: a Serverless plugin
To prevent us from deploying the wrong Git branch to the wrong environment, we added a hook to our deployment, by implementing a Serverless plugin.
You can learn how to write you own Serverless plugins in this blog post.
Here is the code:
What does is pretty simple: it checks the current Git branch by running git rev-parse --abbrev-ref HEAD and blocks the deployment if it does not correspond to the requirement branch for the deployed environment.
To use the plugin, you need to:
- create a
.serverless_pluginsfolder at the same level than yourserverless.ymlconfig file - save the code above in a file
check-git-branch-before-deploy.jsfile in the.serverless_pluginfolder - add the following to your
serverless.ymlconfig file:
service: my-awesome-service
provider:
name: aws
stage: ${opt:stage}
(...)
checkGitBranchBeforeDeploy:
staging: master
production: prod
plugins:
- check-git-branch-before-deployNow, you cannot deploy to the staging environment if you are not on the master branch:
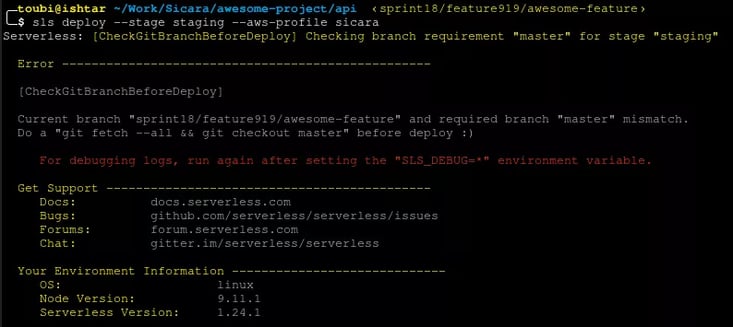
Note that only staging and production environments are protected:
.jpg?width=733&height=169&name=4_e3f9e07ae69813669fe043ab4a0bbc74_800%20(1).jpg)
What’s next?
- Create a repository for the plugin and publish it as a serverless plugins
- Add more checks in the plugin e.g., check that there are no unstaged changes
Thanks to Pierre-Henri Cumenge, Alexandre Chaintreuil, and Flavian Hautbois.
Did you like this article? Feel free to contact us!